New and updated version for Debian Stretch and OCS Inventory NG server 2.5 can be found here!
Introduction
In our first part we have sucessfuly installed and performed basic configuration of OCS-NG 2.2RC1 server. It all works well. We are able to start managing computers and their inventory. Like in first part of series we are using Debian (Jessie) version 8.2. First part can be found here.
However we are unable to use deployment future since it requires a valid SSL certificate both on server and on clients.
Before deploying agent to the clients be sure to test it with SSL certificate installed on server. If they can talk to each other and if client can succesfuly access /download location on the server you’re ready to deploy it on large scale.
IMPORTANT!
For this example we will use a self signed certificate for SSL. If you have your own, trusted root CA or can request a SSL cert I strongly recommend this, since it will be trusted by your OS, so no annoying popups on accessing HTTPS will be displayed about untrusted self signed certificate.
In this tutorial we will perform following steps in order to enable deployment:
- Generate valid SSL certificate using openssl
- Configure Apache2 to use SSL
- Enable SSL on /download folder
- Disable HTTP on /download folder
- Test access with HTTP and HTTPS to deployment share (/download)
- Include/place ocsng certificate in agent config
1. Generate a valid SSL certificate using openssl
First of all we need a SSL certificate. In order to be able to generate it we need a few things on our Debian environment. Let’s start with:
Installation of packages:
apt-get install –y opensslThen we need to enable SSL config for apache:
a2enmod sslAfter this command a new symbolic link called default-ssl.conf will be created in /etc/apache2/sites-enabled/
Ok as we have running openssl we need some certs, don’t we? :)
Following command will generate a key for the certificate:
openssl genrsa -des3 -out ocsng.key 2048Enter and note somewhere (or remember a pass phrase for the key)
Mind, that we are using 2048bit key length because most modern OS will block using keys shorten that that. IETF recommends using at least 2048 or 3072 or even 4096 bit key length since American agency NSA confirmed that they are able to decrypt 1024 keys, so 2048 shouldn’t be a problem in near future.
Back to guide:
Convert the key to RSA:
mv ocsng.key ocsng-old.key
openssl rsa -in ocsng-old.key -out ocsng.keyenter pass phrase
Now, we need a certificate request:
openssl req -new -key ocsng.key -out ocsng.csrFill in all fields:
- Country Name (2 letter code)
- State or Province Name (full name) [Some-State]
- Locality Name (eg, city)
- Organization Name (eg, company) [Internet Widgits Pty Ltd]
- Organizational Unit Name (eg, section)
- Common Name (e.g. server FQDN or YOUR name)
- Email Address
No need to provide extra attributes. There is, however a little trick that can be done. We can provide more than one common name in request to make sure all names are valid: like ocsng.domain.com, ocsng and other dns names or aliases. There is very nice guide how to do that.
If not, simply enter below command to generate certificate in .pem format:
openssl x509 -req -days 3650 -in ocsng.csr -signkey ocsng.key -out ocsng.pemOk now in folder currently in, we have 4 files:
- ocsng.csr
- ocsng.key
- ocsng.pem
- ocsng-old.key
Copy
- ocsng.key to /etc/ssl/private/
- ocsng.pem to /etc/ssl/certs/
by issuing following commands:
cp ocsng.pem /etc/ssl/certs/ cp ocsng.key /etc/ssl/private/Now we need to
2. Configure Apache2 to use SSL
This part is easy and enables apache to use our newly created certificates.
Edit file:
nano /etc/apache2/sites-enabled/default-ssl.confand change lines:
SSLCertificateFile SSLCertificateKeyFileTo:
SSLCertificateFile /etc/ssl/certs/ocsng.pem SSLCertificateKeyFile /etc/ssl/private/ocsng.keyNow, restart apache with command:
service apache2 restartAfter issuing above command a prompt for entering cert key password should be displayed. Enter password for the cert key.
It would be nice to avoid this requirement but not lower the security. We can do that by saving a password in specific executable file located somewhere on the disk:nano /usr/share/apache2/passThis will open nano editor. Paste below code:
#!/bin/sh echo "PASSWORD_FOR_CERT_KEY_GOES_HERE" chmod +x /usr/share/apache2/passPress CTRL+X and Y to save the file.
Now, tell apache to use above file as password:nano /etc/apache2/sites-enabled/default-ssl.confand ADD following:
SSLPassPhraseDialog exec:/usr/share/apache2/passThis will tell apache that upon restart execute file /usr/share/apache2/pass in order to read password.
Ok at this point apache is running with ocsreports that might be accessed with HTTP and HTTPS. This is ok. If you want you can disable HTTP access entirely but I prefer to disable only HTTP access to /download folder. First we need to enable SSL on /download and then, restrict non-ssl session to it:
3. Enable SSL on /download folder
If we have running SSL let’s use it!
edit file:nano /etc/apache2/sites-enabled/default-ssl.confand add following
Alias /download /var/lib/ocsinventory-reports/download <Directory /var/lib/ocsinventory-reports/download> #Options Indexes FollowSymLinks MultiViews AllowOverride None Order allow,deny allow from all </Directory>4. Disable HTTP on /download folder
edit file:
nano /etc/apache2/sites-enabled/ocsinventory-reports.confand replace
Alias /download /var/lib/ocsinventory-reports/download <Directory /var/lib/ocsinventory-reports/download> Order Allow,Deny Allow from all Require all granted </Directory>with this:
Alias /download /var/lib/ocsinventory-reports/download <Directory /var/lib/ocsinventory-reports/download> Order Allow,Deny Deny from all Require all granted </Directory>Now restart apache:
service apache2 restartOk, after completing above steps it’s time to:
5. Test access with HTTP and HTTPS to deployment share (/download)
Try to access address with HTTP:
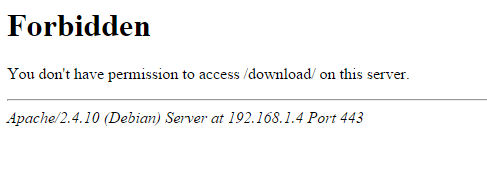
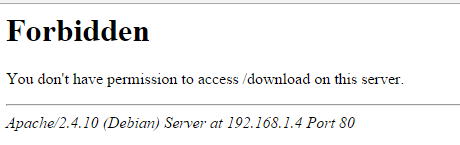
- http://ocsngt-ip-address-or-name/download – you should get a 403 error like:
- Now, try to access a file inside /download folder
Now, try to access /download with HTTPS:
- https://ocsngt-ip-address-or-name/download – you should get a 403 error like:
 It’s ok, since displaying index of /download is forbidden.
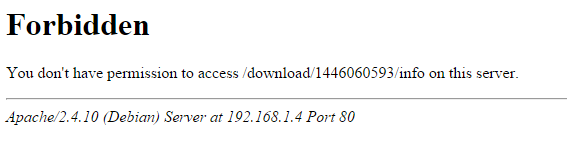
It’s ok, since displaying index of /download is forbidden.- Now try to access a particular file in that directory:
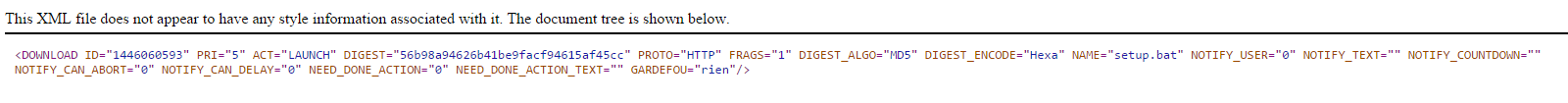
As you can see in above example in this configuration you won’t be able to access /download directory with HTTP at all. Moreover you won’t be able to view listing of that directory either even with HTTPS. But if you know exact name of file and path to it – you (or client agents) will be able to download files that are meant to be deployed on computers. Since client-agents knows that, they will be able to download packages.
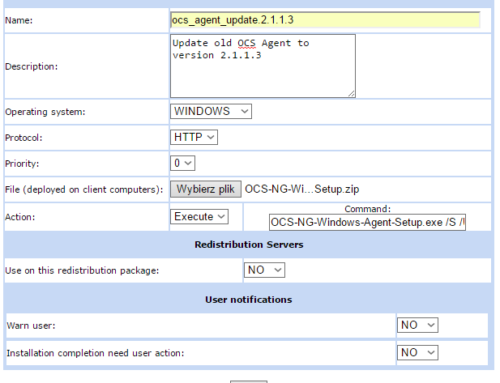
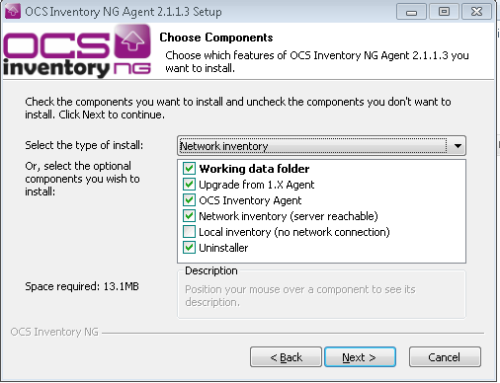
6. Include/place ocsng certificate in agent config
Now as we have working certificate we need to deploy it to agents and tell them to use it in order to be able to communicate and download things from ocs server.
First download the ocsng.pem from your ocs server either by accessing https://fqdn_or_ip_of_ocsserver/ocsreports and saving certificate displayed in your web browser
or
download it directly from server from folder /etc/ssl/certs/ using winscp or similiar tool
Certificate for Windows agent should be placed in:
C:\ProgramData\OCS Inventory NG\Agent\
By default, certificate files is called: cacert.pem
You can change that in ocsinventory.ini file but I recommend to rename ocsng.pem to cacert.pem and place it in above directory. After that, restart the OCS Service by running command as Administrator on your Windows machine:
sc stop "OCS Inventory Service"and then:
sc start "OCS Inventory Service"Now, agent should be able to download packages from OCS server.
Other thing to remember is to change SSL=0 to SSL=1 in ocsinventory.ini! Without that agents will continue to use HTTP which is denied from now. They will be able to detect new package deployment but any download will fail.
There is a way to include couple things in ocs agent install package such as plugins or cert. Just follow this guide to build your own agent install and deploy it with one click!
Conclusion
As you can see there are quite a few commands to be entered before it starts working as it should, but after all as you can see – it’s not that hard. Depend on your needs you may want to restrict HTTP access to OCS server entirely for end users and admins but it is your call. I wouldn’t do that unless you can provide trusted root CA to them (client computer). Otherwise using https with self signed certificate will generate a warning in their web browser each time they access ocs server.
OCS Agents with proper SSL certificate file in their directory will access OCS server without any problems.
As always, please leave a comment!
This is the article that I was searching long time ago!
Excellent. Congrats!
Note: in code-lines in Sections 3 and 4, the characters are incorrect, maybe for the codification of your blog.
Many thanks again!
Hello, thank you for pointing incorrect characters. Fixed, there is a stable version of OCS 2.2 available. I will update this guide to cover it soon as well.
Is this working for the 2.2 official Version?
Thanks
Need to test it since there are quite a few updates in packages in Debian and ocs itself.
Hi great guide for the complete setup.
is it possible to use signed certificates rather than the self-signed certificates?
Ofcourse it is possible as it’s ordinary ssl cert. Just make sure you use .pem format on client machines and make sure you have .pem and .key files available on the server. Also, make sure to specify all subjects/dns/fqdn that server might be access. Otherwise, clients will report bad certificate name :)
Hi Miłosz,
thanks for your work. Unfortenately the /etc/apache2/conf-available/ocsinventory-reports.conf changed a bit. What do I have to change?
# Apache 2.4
Require all granted
Order deny,allow
Allow from all
Alias /download /var/lib/ocsinventory-reports/download
Yeah I know. I wilk be building new instance next weekend so I’ll prepare a new version of the guide
Thank you. It seems, that ssl only need to get activate at ocsinventory-reports.conf.
Yes, you do not need to configure SSL for whole OCS instance, however, if you already have it, why not use it :) ? Anyway, thanks for pointing this out!
Hi Engel,
I can access OCS via https, but the agent cannot get communication with OCS server.
dont restrict the HTTP traffic as initial communication is made with HTTP protocol. Was it working with HTTP proto?
Witam!
Czy istnieje możliwość kontaktu mailowego w razie problemów z instalacją OCS?
Sprawa wygląda tak, że mamy OCS na Ubuntu i chcemy powrzucać agentów na kilka komputerów, tylko do tego wszystkiego będę musiał ogarnąć temat SSL i jakimś cudem to wdrożyć.
Był bym bardzo wdzięczny gdybym mógł od czasu do czasu napisać z pytaniem na maila ponieważ sam jestem raczej początkującym sieciowcem i użytkownikiem Linuxa, dlatego gdy napotkam tu jakiś problem, prawdopodobnie to będzie dla mnie deadend…
Dopisuję maila i liczę na odpowiedź! Pozdrawiam serdercznie
Oczywiście, podesłałem kontakt na Twojego maila. Jeśli będziesz mieć problemy, pisz w miarę możliwości w komentarzach, ponieważ inni również będą mogli skorzystać.
Witam ponownie!
Natrafiłem an problem zaraz po wylaczeniu HTTP w /Download.
Próbuję zrestartować apache2 w/w komendą and odrazu dostaję error:
“Job for apache2.service failed because the control process exited with error code. See “systemctl status apache2.serv ice” and “journalctl -xe” for details.”
Dodam, że w pliku który miałem zmienić troszke inaczej to wyglądało a mianowicie tak:
Order Allow,Deny
Allow from all
Require all granted
Alias /download /var/lib/ocsinventory-reports/download
Więc zmieniłem wartość Allow na Deny a ostatnią linijkę z Alias przeniosłem an górę i pozostawiłem w takiej postaci:
Alias /download /var/lib/ocsinventory-reports/download
Order Allow,Deny
Allow from all
Require all granted
Proszę o pomoc! Słabo znam się na linuxie a muszę to dokończyć…
Pozdrawiam i czekam na odpowiedź!
Cześć a jaki jest output z
systemctl status apache2.serv ice
oraz
journalctl -xe
??
Pierwszy:
apache2.service – LSB: Apache2 web server
Loaded: loaded (/etc/init.d/apache2; bad; vendor preset: enabled)
Drop-In: /lib/systemd/system/apache2.service.d
└─apache2-systemd.conf
Active: failed (Result: exit-code) since Thu 2018-06-14 13:26:04 UTC; 1 weeks
Docs: man:systemd-sysv-generator(8)
Process: 2464 ExecStop=/etc/init.d/apache2 stop (code=exited, status=0/SUCCESS
Process: 9453 ExecStart=/etc/init.d/apache2 start (code=exited, status=1/FAILU
Warning: Journal has been rotated since unit was started. Log output is incomple
~
~
~
journalctl -xe
Jun 25 07:14:32 ip-172-31-38-74 systemd[1]: apache2.service: Unit entered failed state.
Jun 25 07:14:32 ip-172-31-38-74 systemd[1]: apache2.service: Failed with result ‘exit-code’.
root@ip-172-31-38-74:/home/ubuntu# clr
No command ‘clr’ found, did you mean:
Command ‘cl’ from package ‘cl-launch’ (universe)
Command ‘clm’ from package ‘mcl’ (universe)
Command ‘mlr’ from package ‘miller’ (universe)
Command ‘car’ from package ‘ucommon-utils’ (universe)
Command ‘clp’ from package ‘coinor-clp’ (universe)
Command ‘csr’ from package ‘rheolef’ (universe)
Command ‘cyr’ from package ‘console-cyrillic’ (universe)
Command ‘cli’ from package ‘mono-runtime’ (main)
clr: command not found
root@ip-172-31-38-74:/home/ubuntu# clrscr
clrscr: command not found
root@ip-172-31-38-74:/home/ubuntu# clear
root@ip-172-31-38-74:/home/ubuntu# journalctl -xe
— Support: http://lists.freedesktop.org/mailman/listinfo/systemd-devel
—
— Unit UNIT has finished starting up.
—
— The start-up result is done.
Jun 25 07:10:48 ip-172-31-38-74 systemd[30100]: Startup finished in 19ms.
— Subject: System start-up is now complete
— Defined-By: systemd
— Support: http://lists.freedesktop.org/mailman/listinfo/systemd-devel
—
— All system services necessary queued for starting at boot have been
— successfully started. Note that this does not mean that the machine is
— now idle as services might still be busy with completing start-up.
—
— Kernel start-up required KERNEL_USEC microseconds.
—
— Initial RAM disk start-up required INITRD_USEC microseconds.
—
— Userspace start-up required 19140 microseconds.
Jun 25 07:10:48 ip-172-31-38-74 systemd[1]: Started User Manager for UID 1000.
— Subject: Unit user@1000.service has finished start-up
— Defined-By: systemd
— Support: http://lists.freedesktop.org/mailman/listinfo/systemd-devel
—
— Unit user@1000.service has finished starting up.
—
— The start-up result is done.
Jun 25 07:10:53 ip-172-31-38-74 su[30181]: Successful su for root by ubuntu
Jun 25 07:10:53 ip-172-31-38-74 su[30181]: + /dev/pts/0 ubuntu:root
Jun 25 07:10:53 ip-172-31-38-74 su[30181]: pam_unix(su:session): session opened for user root by ubuntu(uid=1000)
Jun 25 07:10:53 ip-172-31-38-74 su[30181]: pam_systemd(su:session): Cannot create session: Already running in a session
Jun 25 07:14:32 ip-172-31-38-74 systemd[1]: Stopped LSB: Apache2 web server.
— Subject: Unit apache2.service has finished shutting down
— Defined-By: systemd
— Support: http://lists.freedesktop.org/mailman/listinfo/systemd-devel
—
— Unit apache2.service has finished shutting down.
Jun 25 07:14:32 ip-172-31-38-74 systemd[1]: Starting LSB: Apache2 web server…
— Subject: Unit apache2.service has begun start-up
— Defined-By: systemd
— Support: http://lists.freedesktop.org/mailman/listinfo/systemd-devel
—
— Unit apache2.service has begun starting up.
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: * Starting Apache httpd web server apache2
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: *
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: * The apache2 configtest failed.
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: Output of config test was:
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: AH00526: Syntax error on line 16 of /etc/apache2/sites-enabled/default-ssl.conf:
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: SSLPassPhraseDialog cannot occur within section
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: Action ‘configtest’ failed.
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: The Apache error log may have more information.
Jun 25 07:14:32 ip-172-31-38-74 systemd[1]: apache2.service: Control process exited, code=exited status=1
Jun 25 07:14:32 ip-172-31-38-74 systemd[1]: Failed to start LSB: Apache2 web server.
— Subject: Unit apache2.service has failed
— Defined-By: systemd
— Support: http://lists.freedesktop.org/mailman/listinfo/systemd-devel
—
— Unit apache2.service has failed.
—
— The result is failed.
Jun 25 07:14:32 ip-172-31-38-74 systemd[1]: apache2.service: Unit entered failed state.
Jun 25 07:14:32 ip-172-31-38-74 systemd[1]: apache2.service: Failed with result ‘exit-code’.
Przepraszam, że tak późno ale wydawało mi się, że z jakiegoś powodu komentarze się nie wysyłają.
Pozdrawiam i bardzo dziękuję za pomoc!
Widzę, że za każdym razem piszesz inny adres email. Dlatego za każdym czeka na approve.
You have syntax error in the apache config file:
AH00526: Syntax error on line 16 of /etc/apache2/sites-enabled/default-ssl.conf:
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: SSLPassPhraseDialog cannot occur within section Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: Action ‘configtest’ failed.
Jun 25 07:14:32 ip-172-31-38-74 apache2[30206]: The Apache error log may have more information.
Czyli chodzi o to PassPhrase? Myslalem ze to cos w rodzaju hasla ktore mam sobie ustalic wiec wpisalem poprostu randomowe haslo ktore zapisałem.
Czy powinienem poprostu edytowac ten plik? A jesli tak to w jaki w jakis sposob, bo zakladam ze to nie bedzie tylko edycja pliku tekstowego.
Pozdrawiam i dziękuję za pomoc!
yes the problem is related to ssl-config file that holds SSL configuration. Error says that you cannot include this directive in this place. I haven’t seen the config file but the Passphrase directive should be included in section among others like:
SSLCertificateFile /etc/ssl/certs/domain.crt
SSLCertificateKeyFile /etc/ssl/private/domain.key
not in section
Witam ponownie!
Mam dość poważny problem, mianowicie po zrobioniu 3 punktu (Enable SSL on /download folder) chciałem sprawdzić coś na ocs i zauważyłem, że nie mogę się z nim połączyć przez ip tak jak wcześniej. W liscie instancji w amazon cloud widzę, że instancja jest włączona, przez putty normalnie się z nią łączę ale OCS nie działa.
Wie Pan może co poszło nie tak lub jak to naprawić?!
Dodam, że używam Ubuntu 16.04.4.
Pozdrawiam.
Good day!
Thanks alot for good article. But i have one issue. i have access to server from http and https. But ocs unix client does not send report to server if i use ssl cert. Without sll all fine. In apache2 log i see POST, in ocs agent log i see “Deflating problem”. (os:Debian 9)
I tryed start agent from console with “–local=…” key – all fine, i got report in folder.
Can you help whit this issue?
Best regard!
Do you have agent set and OCS server set to use SSL? does it only occurs for that particular Unix host or others as well? Can you test SSL on Windows box for example?
Thanks… Excel step by step …
cześć. mam problem, mianowicie po dodaniu wpisu
Alias /download /var/lib/ocsinventory-reports/download
#Options Indexes FollowSymLinks MultiViews
AllowOverride None Order
allow,deny allow from all
do ssl.conf (używam centosa7) dostaję taki błąd:
Job for httpd.service failed because the control process exited with error code. See “systemctl status httpd.service” and “journalctl -xe” for details.
możesz podpowiedzieć co jest nie tak ?
dzięki
Cześć, zawsze najpierw testuj sobie konfigurację apache’a przed zrestartowaniem, dodatkowo w komendach, które są podane jako “see” będzie dokładny błąd serwera.
Moim zdaniem nowe linie są pomieszane, zobacz sobie tutaj jak to wygląda na działającym przykładzie:
https://miloszengel.com/ocs-inventory-ng-2-5-install-guide-on-debian-stretch-with-ssl-and-deployment/5/
as per your document configured ssl certificate and agent connected with ssl. now deployment package activated from server to client but it;s showing WAITING NOTIFICATION. can not work deployment. can you guide how to deploy any package or shell script to linux machine from ocs server. i am waiting for your replay.
it may be related to deployment settings on server. Seems like notification url is wrong. Please look at newest version of this guide.